This post has been revised since it was initially published on 31st March due to errors found in the resulting build. It was also missing details on the shared data drive between the two machines, so has been amended to include that.
** WARNING ** This works for me – it might not for you!
The outcome of this build will leave you with the following:
Boot up, go through the VeraCrypt bootloader, enter a password for Windows, or press escape to load the Grub bootloader where you will boot (K|L|X|)Ubuntu(| Mate| Gnome).
The Windows environment will be encrypted with VeraCrypt, an open source Full Disk Encryption technology, while the Linux environment will be encrypted using Luks. The shared volume (between Windows and Linux) will be encrypted with VeraCrypt.
PLEASE BE AWARE THAT ANY WINDOWS 10 UPGRADES WILL FAIL TO APPLY AS IT WILL NOT RECOGNISE THE VERACRYPT FILE SYSTEM! To resolve this, decrypt the Windows volume, perform the upgrade, re-encrypt it, then transfer the new recovery ISO image to the boot volume, following the method below. Yes, this will take some time. No, you don’t need to decrypt the data volume. Yes, you can use that data volume to shunt the ISO image around.
LATE EDIT 2020-01-06: I’ve just spotted a link to this post over on Level1Techs. In that post, someone asked if the broken upgrades is still a thing. Turns out that since I wrote this in 2017, it’s not been fixed. Now, I should stress, I’ve stopped using this layout as I went all-Linux on that machine, but… it might work for you now?! Also, shout out to 92aceshigh for referencing this post, and glad something I wrote helped you! ☺
Step 1:Create your partition table
My partition table, for a 320GB Disk looks (roughly) like this:
Partition 1: 20GB – Linux /Boot (ext2, plus space for ISO files for random booting)
Partition 2: 60GB – Windows C:\ (NTFS VeraCrypt)
Partition 3: 72GB – Linux Physical Volume (LVM PV, Luks Encrypted)
– logical volume 1: 16Gb Swap (Linux Swap)
– logical volume 2: 60Gb Linux (ext4)
Partition 4: 156GB – Shared Volume (NTFS, VeraCrypt)
I performed this using GParted in the Gnome Live image using the GParted. Some rational here:
- The first partition also allows me to add other ISOs if I want to boot them.
- I have 4GB RAM, this gives me some extra space to allow me to hibernate, but also… 4Gb. Ugh.
- I then split my Linux and Windows partitions into two equal parts.
Step 2: Use Cryptsetup to format the disk
The following steps need to be run as root.
sudo -i
Step 2a: Format the partitions as LUKS
cryptsetup luksFormat -y -v /dev/sda3
Step 2b: Open the LUKS volume
cryptsetup luksOpen /dev/sda3 lvm-pv
Step 2c: Create the LVM Physical Volume over the LUKS volume
vgcreate vg00 /dev/mapper/lvm-pv
Step 2d: Define the LVM Logical Volumes over the LVM Physical Volume
lvcreate -n lv00_swap -L 16G vg00 # Define 16GB Swap Space
lvcreate -n lv01_root -l +100%FREE vg00 # Define the rest of vg00 as /
LEAVE YOUR TERMINAL OPEN
Step 3: Install your Linux distribution.
Note that when you perform your install, when you get to the partitioning screen, select “Manual”, and then pick out the following volumes:
/dev/mapper/vg00-lv01_root = ext4 formatted, mount point: /
/dev/mapper/vg00-lv00_swap = swap
/dev/sda1 = ext2, format, mount point: /boot
Select the boot volume of /dev/sda. But wait, I hear you say, Windows has a well know history of nuking Grub partitions… Well, we’ll sort that in a bit…
DON’T EXIT THE LIVE SESSION ONCE THE INSTALL HAS FINISHED (select “Continue Testing”).
Step 4: Make your machine actually able to boot
Go back to your terminal session. It should still be logged in as root. We need to re-mount all the partitions…
Step 4a: Mount your volumes
mount /dev/mapper/vg00-lv01_root /target
mount /dev/sda1 /target/boot
for i in /dev /dev/pts /proc /sys /run; do sudo mount -B $i /target$i; done
Step 4b: Swap to the “Target” filesystem
chroot /target
Step 4c: Setup your volumes to prompt for cryptographic keys
echo "LinuxRoot UUID=`blkid | grep sda3 | cut -d\\\" -f2` none luks" > /etc/crypttab
Step 4d: Update the boot volume to use these changes
update-initramfs -u
Step 4e: Ensure Grub is also installed to the MBR for testing
grub-install --force /dev/sda1
chattr +i /boot/grub/i386-pc/core.img
update-grub
The first part installs grub to the boot position, even though it doesn’t like it, and the second forces the core file to be unchangeable… I’m not exactly sure of the impact of this, but it’s the only way to do the next part of this process. The last bit makes sure that you’ve got the latest grub config files installed.
Step 5: Reboot and test
Just check to make sure the machine boots OK!
You should have a booting Ubuntu derivative with an encrypted file system. Awesome.
Now let’s install Windows!
Step 6: Install Windows and Veracrypt.
You should boot from your install media, when you get to the partition selector, there should only be a single NTFS partition for it to use. Use it.
Install the latest version of Veracrypt from https://veracrypt.codeplex.com/
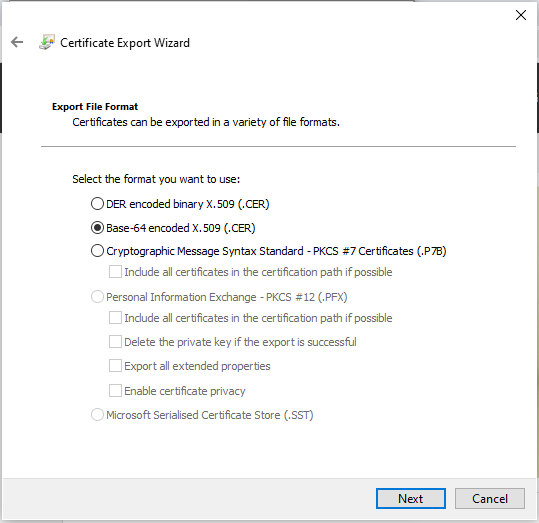
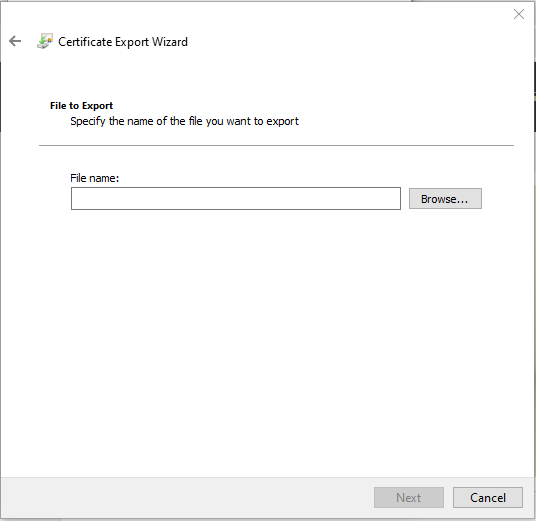
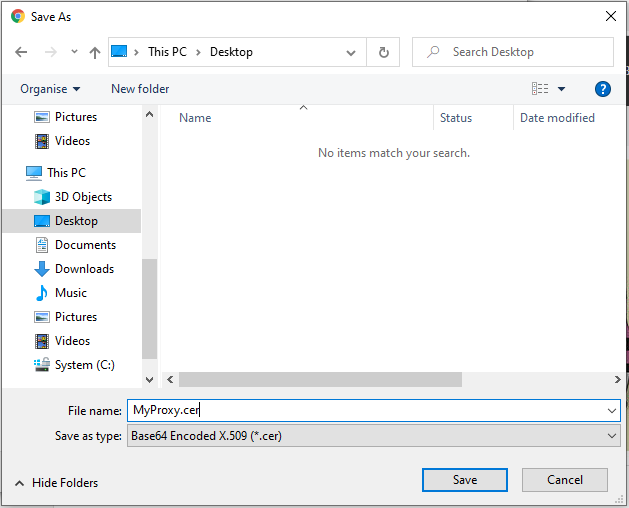
Once it’s installed, go to System, Encrypt System Partition/Drive, “Normal” system encryption, Windows System Partition, Multi-Boot (accept the warning), Boot Drive “Yes”, Single Disk, “Non-Windows Boot Loader” – No, and then… let it go through all the rest of the steps. There will be one stage where it asks you to create a rescue disk. Just save it for later. Once the encryption settings are collected, it will do a test (which is basically just rebooting to the boot loader, having you put in your password and going back into Windows), and then let it start performing the encryption.
Once the encryption finishes, reboot the computer, enter the decryption password and test it boots to Windows OK. Then reboot it again and press escape instead of putting in the password. It will boot to your Ubuntu system.
So, there you have it. One Dual-Boot system with encrypted disks everywhere!
Step 7: Setting up the shared volume.
After you’ve got the Ubuntu and Windows volumes sorted out, next we need the shared data volume to be organised. You’ll need Veracrypt for Ubuntu. Use the following to install the Veracrypt package for Ubuntu:
sudo add-apt-repository ppa:unit193/encryption
sudo apt-get update
sudo apt-get install veracrypt
Once that’s installed, boot back into Windows and create a new volume – perhaps V: for Veracrypt, or E: for Encrypted – your choice, but make sure you create it using the same password that you used for the Windows partition.
Format this new volume with either NTFS or FAT32 so that you can mount it under either operating system. I chose NTFS.
Now, you need to go into Veracrypt’s Settings menu, and select “System Encryption Settings”. Tick “Cache pre-boot authentication password in driver memory” (be aware, this means that if your machine is compromised when powered up, the password could be recovered), then OK. This may prompt you to accept the UAC at this point.
Next, with the mounted volume selected, go to the “Favorites” menu, and choose “Add to System Favorites”. In the screen which comes up, select the box under “Global Settings” which says “Mount system favorite volumes when Windows starts (in the initial phase of the startup procedure)”. There will be a warning about passwords that appears. Click OK.
You may, at this point, want to move certain aspects of your Windows desktop (e.g. the “My Documents” location) to the new mounted drive.
On the Linux OS, become root, with sudo, and then add the following lines to your crontab:
@reboot mkdir -p /shared_storage
@reboot veracrypt --text --non-interactive --fs-options=uid=1000,gid=1000,umask=0077 --password="YOURSUPERSECUREPASSWORD" /dev/sda4 /shared_storage
These assume that your login user’s ID is 1000 (you can check that by running the command “id” as your logged in user), that you want to use “/shared_storage” as the mount point (it stops Ubuntu treating it as a “Mountable Volume” if it’s not in your home directory and not in /mnt or /media). These options also mean that only that user (and root) can access any of the files in that partition (although, it is only you on this laptop… right?), which means you can safely use it for any files which check user permissions before allowing you to access them (e.g. SSH keys). I then set up a symbolic link to /home/MYUSERACCOUNT/Documents into the /shared_storage/Documents directory, and /home/MYUSERACCOUNT/.ssh into the /shared_storage/SSH_Keys directory.
Citataions
The following list of resources helped me out when I was struggling with what to do next! They may not be canonical sources, but they helped.
- http://thesimplecomputer.info/full-disk-encryption-with-ubuntu – This is what got me started on this little journey!
- http://askubuntu.com/questions/161689/how-do-i-get-grub2-to-boot-a-truecrypt-encrypted-mbr – How to add the Veracrypt recovery disk to your Grub boot partition. Note, I do it slightly differently to this now.
- http://askubuntu.com/questions/711801/i-deleted-files-in-boot-now-cant-boot-linux – I may have done this. It tells you how to put all your important files back for booting purposes :)
- https://www.youtube.com/watch?v=Z1yWbBIqh1o – Walk through of installing Veracrypt to Windows 10. I used this to see some of the terms after I’d already installed Veracrypt. I don’t quite follow the same route as him though.
- https://www.linux.com/blog/how-full-encrypt-your-linux-system-lvm-luks – Using LVM inside Luks for the full-Linux disk (this was why I’ve re-written this post)
- https://wiki.archlinux.org/index.php/Dm-crypt/Encrypting_an_entire_system – Some details around how the Luks stuff all works
I may or may not have reinstalled Windows and Kubuntu about 20 times during this process, cursing myself for starting the whole damn process off in the first place!!!